Understanding BLS Signatures
A Guide for Solidity Developers and Auditors
As the blockchain ecosystem evolves, we continuously push the boundaries of cryptographic tools that enhance security, scalability, and interoperability. One such tool gaining prominence, particularly in the Ethereum ecosystem, is the Boneh-Lynn-Shacham (BLS) signature scheme.
BLS signatures are critical for distributed systems, enabling cryptographically secure aggregation of signatures. This article dives into the technical aspects of BLS signatures, targeting Solidity developers and auditors who are keen to understand how this technology can be implemented and audited.
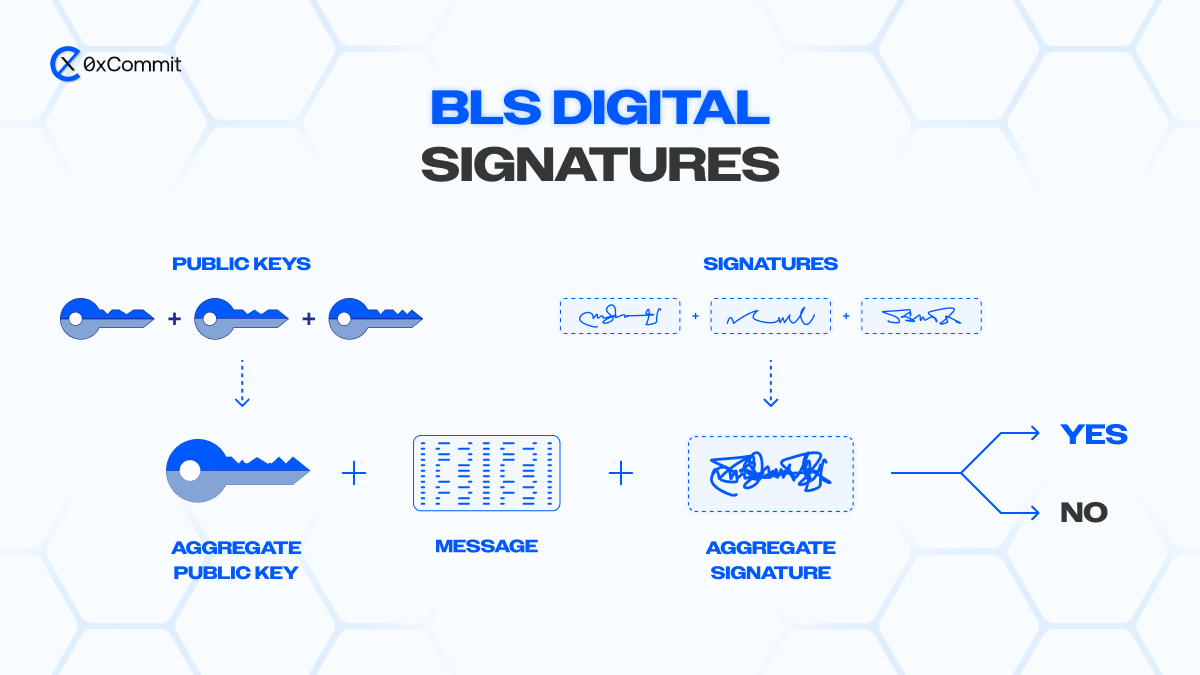
What Are BLS Signatures?
At their core, BLS signatures are cryptographic digital signatures designed for signature aggregation. Unlike traditional signatures (e.g., ECDSA used in Ethereum), BLS signatures allow multiple signatures on the same message to be aggregated into a single signature. This results in reduced storage and verification costs while maintaining the cryptographic guarantees of the original signatures.
BLS signatures are particularly useful in scenarios involving:
Multi-signature wallets
Validator committees
Layer 2 rollups
Cross-chain interoperability
They are leveraged in projects like Ethereum 2.0 for aggregating validator signatures into a single succinct proof during block proposals.
Key Properties of BLS Signatures
Signature Aggregation: Multiple signatures on the same or different messages can be aggregated into a single signature.
Efficient Verification: An aggregated signature can be verified as quickly as a single BLS signature. This is useful for improving throughput on blockchain networks.
Deterministic: BLS signatures are deterministic, meaning the signature generated from the same private key and message will always be the same. This is unlike ECDSA, which requires a random nonce for each signing operation.
Provable Security: BLS signatures are based on pairing-based cryptography, relying on the Computational Diffie-Hellman problem (CDH), ensuring strong security guarantees.
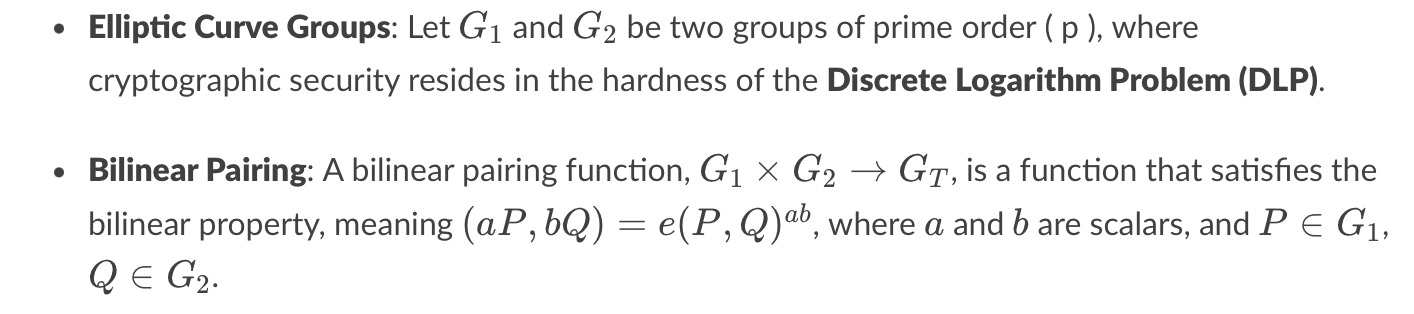
BLS Signature Scheme: Mathematical Foundations
To appreciate how BLS signatures work, we need a basic understanding of pairing-based cryptography. Here’s an outline of the math behind the BLS signature scheme:
This pairing operation enables aggregation of signatures, which is the backbone of BLS.
BLS Signature Steps:
Key Generation:
Signature Generation:
Signature Verification:
To verify a signature σ\sigmaσ on a message mmm for a public key pkpkpk, check that the following pairing holds:
e(σ,P)=e(H(m),pk)
If this equation holds, the signature is valid.
Implementing BLS Signatures in Solidity
As of now, Solidity does not natively support the complex pairing-based cryptography required for BLS signatures, but libraries like ethereum/py_ecc provide the necessary tools for implementing and verifying BLS signatures in a Web3 context. Additionally, Solidity's bn256 precompile can help verify pairings, though it might not directly support BLS signatures without further modification.
For Ethereum 2.0 development, much of the BLS signature handling happens off-chain. Auditors and developers must focus on correctly verifying signatures and ensuring the correctness of BLS signature operations implemented within smart contracts.
BLS Signature Verification in Solidity
While Solidity does not directly provide built-in functions for BLS, developers can use the bn128 pairing precompile (available at address 0x08). Here’s a simple code snippet that performs BLS signature verification using pairing:
pragma solidity ^0.8.0;
contract BLSVerification {
// Precompile address for bn256 pairing operation
address constant PAIRING_PRECOMPILE = 0x08;
function verifyBLS(
bytes32[2] memory signature,
bytes32[2] memory pubkey,
bytes32 message
) public view returns (bool) {
// Implement your custom BLS verification logic
// You can use bn256 for pairings but will need
// off-chain help for full BLS verification
//
// pairingCheck = e(signature, G2) == e(H(message), pubkey)
return true; // Example placeholder
}
}Security Considerations:
Ensure that the hash function used (e.g., SHA-256 or Keccak256) is resistant to birthday attacks, as collisions could invalidate the uniqueness of the message-signature pair.
Pay attention to gas costs when implementing pairing operations, as they can be computationally expensive.
Auditing BLS Signatures
When auditing smart contracts that incorporate BLS signatures, several key points need to be scrutinized:
Correctness of Aggregation: Ensure that the contract correctly aggregates and verifies signatures. Mistakes in the pairing check can lead to signature forgery vulnerabilities.
Efficient Use of Precompiles: Smart contracts should correctly interface with Ethereum's precompiles for pairing checks. Improper use can result in excessive gas consumption or failed verifications.
Hashing into G1: Developers need to ensure that the hash function used maps securely into the elliptic curve group G1G_1G1. Misimplementation of this step can compromise the security of the BLS signature.
Gas Optimizations: Pay close attention to the gas costs associated with pairing operations. While bn256 precompiles are more efficient than pure Solidity, they still incur high gas costs, especially with multiple signature verifications.
Conclusion
BLS signatures offer a powerful tool for Solidity developers, enabling signature aggregation, which can vastly improve the scalability of blockchain systems. However, the cryptographic complexity of BLS signatures necessitates careful implementation and auditing. Solidity developers and auditors must focus on correct usage of precompiles, ensure secure hashing mechanisms, and optimize gas consumption when incorporating BLS signature verification into smart contracts.
As BLS signatures become integral to Ethereum 2.0 and other projects, understanding their intricacies will be essential for building scalable, secure smart contracts and ensuring that decentralized systems can support massive user bases without compromising performance or security.
Reference: